We live in a same-day-delivery, TikTok-attention-span culture, so it’s no surprise most folks don’t have the patience for most cybersecurity best practices.
Remembering a unique password for each online account (the average person has 87) eats up mental energy. Clicking through multifactor authentication slows workflows and delays instant gratification people crave. Adopting passkeys requires people to offer up biometric data they’re afraid hackers will steal (it happens).
So, it’s not surprising that people cut corners and settle for convenience over security. And that’s a major mistake.
As a security-focused MSP, we see the fallout when people choose convenience over protection. Best case scenario? A single computer in the chain gets compromised and data is lost to ransomware. Worst case scenario? A single incursion results in enterprise-wide breaches with millions in fines and losses.
That said, we’re not suggesting organizations quadruple authentication and quarantine all your data assets. Here’s how your organization can strike a balance between security and accessibility.
Key Takeaways (Your TL;DR)
- Balancing cybersecurity and convenience is critical since too much friction drives risky workarounds while too little security invites breaches.
- Passwords alone are no longer effective against AI-powered attacks and credential-stuffing tools.
- MFA, passkeys, and context-aware authentication reduce risk while preserving productivity.
- Smart security focuses on protecting high-value systems without locking down every workflow.
AI Is Eating Your Passwords for Breakfast
For decades, cybersecurity experts tried to convince users to build burly passwords. You’ve probably received passive-aggressive (and aggressive-aggressive) messages trying to convince you to follow these three rules:
- Never use any of the top 10 common passwords
- Avoid password reuse
- Create secure, memorable passwords
If you’re following them, that’s a great start. But honestly, these password best practices aren’t enough anymore. Especially because AI is becoming a really good guesser.
Criminals have trained AI models on billions of leaked credentials from past breaches, giving them the fodder to recognize common password phrases or even spot patterns. ML tools perceive that people love to sprinkle favorite sports teams, childhood pets, or major anniversaries into passwords. If they’re given the target’s personal data from other online breaches, AI can generate eerily good guesses.
Today, what took years or months to guess takes minutes or seconds. The Ethical Hacking Institute finds that PassAI outperforms dictionary attacks (attacks that systematically try words and phrases) threefold and CrackNet guesses 60% of common passwords in seconds.
There’s even a risk that 64-character passwords will one day lose their security as quantum computing develops. But that’s an article for another (hopefully distant) day.
So, what’s the alternative?
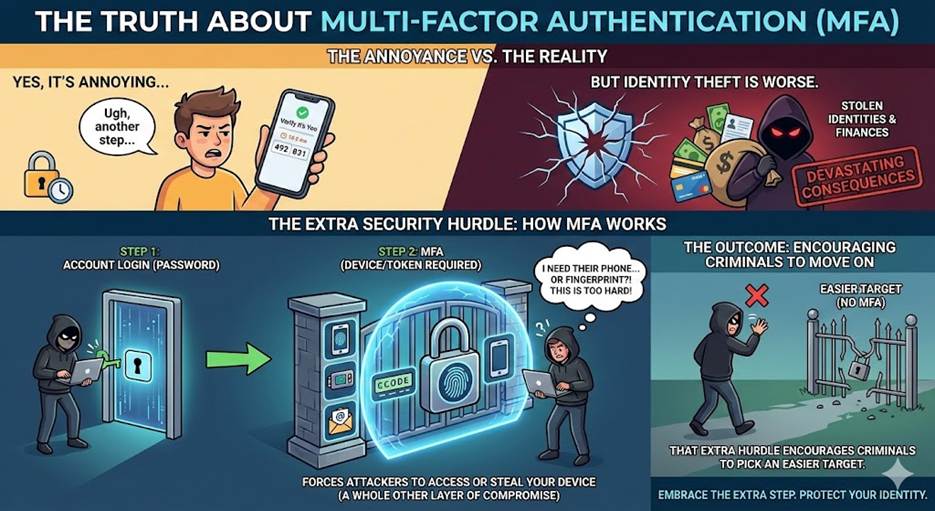
First, embrace multi-factor authentication (MFA). Yes, it’s annoying. But identity theft is worse. MFA forces attackers to remotely access or steal your device (not just your account), which requires a whole other layer of compromise. That extra hurdle can encourage criminals to pick an easier target.
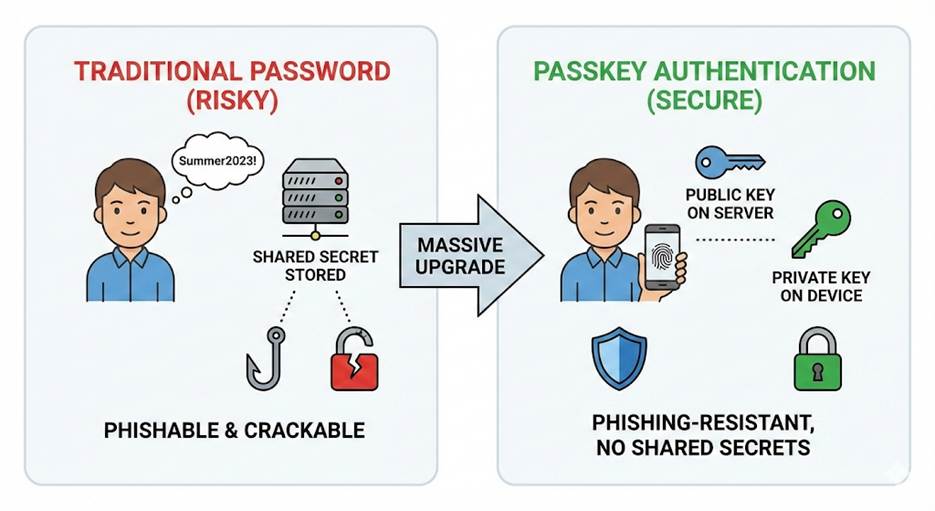
Second, adopt passkeys and phishing-resistant authentication. For those not in the know, passkeys are a form of passwordless logins, whether it’s a phone or another device, that can be used to authenticate a user’s identity. Passkeys are more secure because they provide phishing-resistant authentication and eliminate the shared secrets or passwords that can be cracked. It’s not perfect, but it’s a massive upgrade from “Summer2023!”
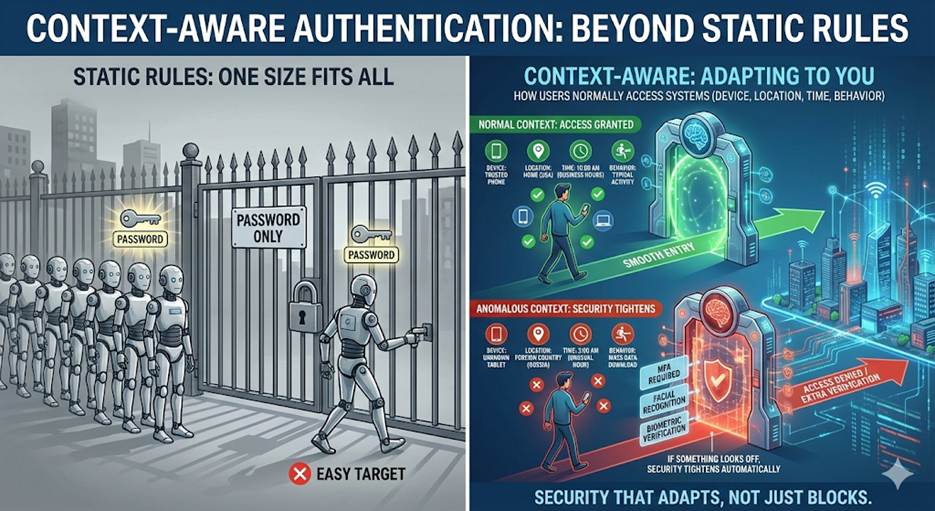
Third, explore context-aware authentication instead of static rules. Basically, how users normally access systems (i.e. device, location, time, behavior, etc.) If everything looks normal, access is granted. If something looks off, security tightens automatically.
These approaches reduce friction, limiting them to moments that actually matter and keeping users safe without making their lives too much harder.
When You Can Ease Up (Yes, Really)
Now for the part that surprises people. You don’t need Fort Knox levels of security everywhere. Some systems require intense monitoring; others don’t. Treating all data equally is how you end up with employees revolting or workflows grinding to a halt.
Some examples where you can responsibly ease up:
Low-risk internal tools
Does an app not touch sensitive data? Is it separate from core systems? Would it going down not ruin your week? It may not need ironclad controls. Use sensible authentication, but don’t stack hurdles just because you can.
Read-only access
Viewing data is very different from exporting, modifying, or deleting it. Ramp up security for high-impact actions. Loosen it for passive ones.
Well-segmented environments
If your network is properly segmented (and that’s a big if), breaches don’t automatically turn into disasters. Strong segmentation gives you room to balance convenience without betting the company.
This is what smart security looks like. Not “lock everything forever,” but “protect what matters most.”
The Real Goal: Security People Actually Use
If logging in feels like defusing a bomb in a Mission: Impossible movie, users will find shortcuts. And attackers love shortcuts. So, it’s important to understand the risks to your people and workflows and then weigh your tolerance for friction.
At the end of the day, cybersecurity is a balancing act. One part risk management. One part human psychology. One part knowing where attackers actually focus their efforts. Cubex Group helps organizations walk that tightrope.
We design security strategies that protect what matters most without turning everyday work into a grind. We know where AI is changing the threat landscape. We know where convenience is worth the tradeoff. And we know how to build defenses people won’t sabotage out of frustration.
Because in the real world, security only works if it works for your business. And nobody has time for another password reset email anyway.
Looking for help with your cybersecurity? Cubex Group Security Solution (CGSS) offers the right amount of protection, scaling with your needs and threats.
Related Articles
What Is the Difference Between EDR and MDR in Your Cybersecurity Solutions?
Law Firm Prevents Phishing Attack with Cubex Group Security Solution
How a Staffing Firm Enhanced Their Cybersecurity to Protect Clients, Candidates, and Employees
